
domain
Docker, an advanced chroot utility
Fri, 11/29/2019 - 19:09 — Alexis Wilke
SECURITY WARNING
Before installing Docker and containers with services on your Linux system, make sure to read and understand the risks as mentioned on this Docker and iptables page. Especially, Docker will make all your containers visible to the entire world through your Internet connection. This is great if you want to indeed share that service with the rest of the world, it's very dangerous if you are working on that container service since it could have security issues that need patching and such. Docker documents a way to prevent that behavior by adding the following rule to your firewall:
iptables -I DOCKER-USER -i eth0 ! -s 192.168.1.0/24 -j DROP
This means that unless the IP address matches 192.168.1.0/24, the access is refused. The `eth0` interface name should be replaced with the interface name you use as the external ethernet connection. During development, you should always have such a rule.
That has not worked at all for me because my local network includes many other computers on my LAN and this rule blocks them all. So really not a useful idea.
Instead, I created my own entries based on some other characteristics. That includes the following lines in my firewall file:
*filter :DOCKER-USER - [0:0] -A DOCKER-USER -j early_forward -A DOCKER-USER -i eno1 -p tcp -m conntrack --ctorigdstport 80 --ctdir ORIGINAL -j DROP -A DOCKER-USER -i eno1 -p tcp -m conntrack --ctorigdstport 8080 --ctdir ORIGINAL -j DROP -A DOCKER-USER -i eno1 -p tcp -m conntrack --ctorigdstport 8081 --ctdir ORIGINAL -j DROP
My early_forward allows my LAN to continue to work. These are my firewall rules that allow my LAN computers to have their traffic forwarded as expected.
Then I have three rules that block port 80, 8080, and 8081 from Docker.
Docker will add new rules that will appear after (albeit not within the DOCKER-USER list) and will open ports for whatever necessary service you install in your Dockers.
Note that the only ports you have to block are ports that Docker will share and that you have otherwise open on your main server. If Docker opens port 5000 and your firewall does not allow connections to port 5000 from the outside, then you're already safe. On my end I have Apache running so as a result I block quite usual HTTP ports from Docker.
Docker
As we are helping various customers, we encounter new technologies.
In the old days, we used chroot to create a separate environment where you could have your own installation and prevent the software from within that environment access to everything on your computer. This is particularly useful for publicly facing services liek Apache, Bind, etc.
Brief Overview of CRISC Certification Exam
Sat, 06/23/2018 - 14:08 — Alexis WilkeThe CRISC, also known as Certified in Risk and Information Systems Control, is a vendor-neutral certification that validates a professional’s knowledge and experience in the fields of information system control & risk management. The certificate is developed and administered by ISACA and designed for the individuals who work with organizations in mitigating business risks and implement information system controls.
Organizations in today’s world must consistently enhance their infrastructure so that they can survive and thrive in today’s competitive environment. It is a ...
Domains For Sale
Once in a while Made to Order Software Corporation has a domains for sale. You will find here the list of such domains when some are available. Click on the links to contact us in regard to such and such domain.
If you have any question in that regard, feel free to contact us.
Bad Google Indexing "Secure" Pages...
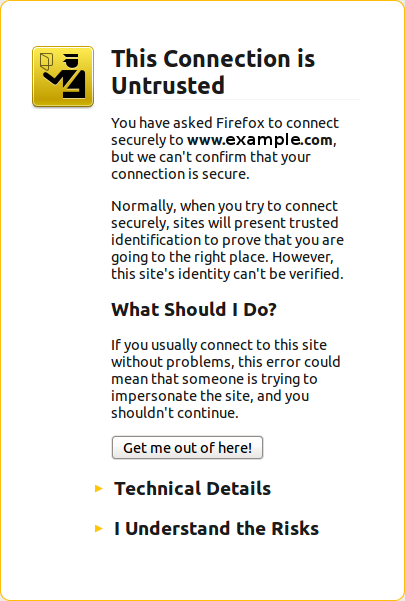
Wed, 08/22/2012 - 20:45 — Alexis WilkeAbout a week ago I got a customer who started having their website appear in Google with HTTPS (the secure version of the site.) The pages are served securily, but it uses our website certificate so you get a big bad error saying that everything is broken and if you proceed you'll know what hell is like.
 The fact is that this customer never had a secure certificate. In other words, there is no reason for the site to have been referenced with HTTPS unless someone typed a link to their site and inadvertendly entered https://... instead of http://...
The fact is that this customer never had a secure certificate. In other words, there is no reason for the site to have been referenced with HTTPS unless someone typed a link to their site and inadvertendly entered https://... instead of http://...
I checked a few of the pages where there ...
South Sudan top-level domain is .ss
Tue, 09/13/2011 - 11:20 — Alexis WilkeVery recently, Sudan was split in the northern and southern part. The southern part has a new name: South Sudan. It is now official and the new ISO country code given to this new country is SS.
This means their country top-level domain name will be .ss.
Assuming they open their domain name to all world wide, this is going to be quite interesting! There are many words in the English language that end with .ss such as dre.ss, and stre.ss, and le.ss...
If you're in the domain name business, look out for those! If it works like other top-level domains, these will go really quick and make ...
MobileKey global settings
The MobileKey module comes with the following settings. These settings are found here:
Administer » Site configuration » MobileKey
Front Page Redirect
Since you generally give one URL to your users, your home page (called Front Page in Drupal), it can be practical to send Mobile phone users to a special URL so when they access your site they see a better adapted front page than the usual.
The settings accept a local path (i.e. mobile) or a full path (i.e. http://mobile.example.com/).
Note that this gives you a way to use the ThemeKey capability to change the theme of all ...
What Country is this Domain Name Extension from?
Sat, 04/17/2010 - 17:38 — Alexis WilkeDomain Descriptions
Got a URL with a weird extension at the end (i.e. not a .com, .org, .info, .tv...) Wondering where that extension is from? Some, you may know because it is the usual country code, such as .de, .fr or .it. Others are harder to know because you probably did not learn the name of the some 276 countries of the world (know of .fm, .vc, .vg, .ws and .ng?)
Discuss This! module Known Issues
The module works and is secure, however, there are problems difficult to circumvent. The following lists them. If you can help fixing some them, you'll be more than welcome!
Reordering the Comments on your Node
It is possible to reorder the node fields using the CCK module. If the Discuss This! comments do not appear exactly where you'd expect them to be, try using the the CCK module:
- Download the CCK module
- Install the CCK module
- Go to Administer » Content management » Content types
- Click on Manage content fields next to the node type you are ...
Insert Node Usage
Syntax
The Insert node tag syntax is:
[node:<name of node> <parameters>]Name of node
The <name of node> can either be
FileAttributes
The FileAttributes tag is new to version 8. It must be present in all movies version 8 and over. It must be the very first tag in the SWF movie. It should be unique (other instances will be ignored.)
The f_has_metadata flag shall be set to 1 whenever the movie includes a Metadata tag.
The f_allow_abc flag shall be set to 1 to give the player the right to execute DoABC scripts (this is a version 9 flag, in version 8, keep it set to 0.)
The f_suppress_cross_domain_caching must have some effect over the caching of some things... (version 9+)
The f_swf_relative_urls means that URLs specified ...
